 Graham Cluley at Sophos recently wrote an excellent history of Apple Macintosh malware. He points out that Mac malware is a subject that raises strong emotions. There are some who believe that the problem is over-hyped and others who believe that the malware problem on Macs is underestimated by the Apple-loving community. The author writes that hopefully, this short history will go some way to present the facts and encourage sensible debate. (rb- We have just taken on a new customer which is 85% Mac and 15% PC. I have had this very conversation with my Apple certified tech who does the field support.)
Graham Cluley at Sophos recently wrote an excellent history of Apple Macintosh malware. He points out that Mac malware is a subject that raises strong emotions. There are some who believe that the problem is over-hyped and others who believe that the malware problem on Macs is underestimated by the Apple-loving community. The author writes that hopefully, this short history will go some way to present the facts and encourage sensible debate. (rb- We have just taken on a new customer which is 85% Mac and 15% PC. I have had this very conversation with my Apple certified tech who does the field support.)
Click here to read part 1 of the History of Mac Malware. Click here to read my recent series commemorating the 25th anniversary of the computer virus.
![]() Big changes to the Mac malware scene arrived with the release of Mac OS X – a whole new version of the operating system which would mean that much of the old malware would no longer run. All future, Mac-specific malware would have to be written with a new OS in mind.
Big changes to the Mac malware scene arrived with the release of Mac OS X – a whole new version of the operating system which would mean that much of the old malware would no longer run. All future, Mac-specific malware would have to be written with a new OS in mind.
2004 – The Renepo script worm (also known as “Opener”) attempted to disable Mac OS X security including the Mac OS X firewall. The author reports that the Renepo worm would download and install hacker tools for password-sniffing and cracking, make key system directories world-writable, and create an admin-level user for hackers to later abuse.
 In 2004, hackers also wrote a proof-of-concept program called Amphimix which demonstrated how executable code could be disguised as an MP3 music file on an Apple (AAPL) Mac. Amphimix appeared to been written as a proof-of-concept highlighting a vulnerability in Apple’s software.
In 2004, hackers also wrote a proof-of-concept program called Amphimix which demonstrated how executable code could be disguised as an MP3 music file on an Apple (AAPL) Mac. Amphimix appeared to been written as a proof-of-concept highlighting a vulnerability in Apple’s software.
2006 – The first virus for Mac OS X was discovered in 2006. OSX/Leap-A was designed to use the Apple iChat instant messaging system to spread itself to other users. As such, it was comparable to an email or instant messaging worm on the Windows platform.
![]() The author concludes that it was correct to call OSX/Leap-A a virus or a worm. It was not correct to call OSX/Leap-A a Trojan horse. Not that that stopped many in the Mac community claiming it wasn’t a real virus.
The author concludes that it was correct to call OSX/Leap-A a virus or a worm. It was not correct to call OSX/Leap-A a Trojan horse. Not that that stopped many in the Mac community claiming it wasn’t a real virus.
2007 – Sophos discovered an OpenOffice multi-platform macro worm capable of running on Windows, Linux, and Mac computers. The BadBunny worm dropped Ruby script viruses on Mac OS X systems and displayed an indecent JPEG image of a man wearing a rabbit costume.
 The first financial malware for Mac appeared in 2007. The OSX/RSPlug-A Trojan horse was first detected by researchers at Intego. Mac users infected themselves by downloading and running a fake codec that claimed to help users view pornographic videos. Once on a victim’s Mac, RSPlug changed that machine’s DNS settings so that, while browsing the web, users would redirect to phishing sites or sites containing advertisements for other pornographic sites.
The first financial malware for Mac appeared in 2007. The OSX/RSPlug-A Trojan horse was first detected by researchers at Intego. Mac users infected themselves by downloading and running a fake codec that claimed to help users view pornographic videos. Once on a victim’s Mac, RSPlug changed that machine’s DNS settings so that, while browsing the web, users would redirect to phishing sites or sites containing advertisements for other pornographic sites.
According to Kasperskey’s Threat Post, RSPlug’s various incarnations are all forms of the DNSChanger malware. DNSChanger featured prominently as the target of the FBI’s 2011 take-down of the malware network, dubbed Operation Ghost Click.
2008 – Apple malware became more sophisticated in 2008. Cybercriminals targeted Mac and PC users in equal measure, by planting poisoned ads on TV-related websites. If accessed via an Apple Mac, surfers would be attacked by a piece of Macintosh scareware called MacSweeper. Close relatives of MacSweeper including Imunizator, claimed to find privacy issues on the user’s computer.
The author details the growing sophistication of Mac malware in 2008.
 The OSX/Hovdy-A Trojan horse would steal passwords from Mac OS X users, open the firewall to give access to hackers, and disable security settings.
The OSX/Hovdy-A Trojan horse would steal passwords from Mac OS X users, open the firewall to give access to hackers, and disable security settings.- Troj/RKOSX-A a Trojan horse is a Mac OS X tool to assist hackers to create backdoor Trojans, which can give them access and control over your Apple Mac computer.
- The Jahlav Trojan was similar to other malware campaigns, cybercriminals created a bogus webpage claiming to contain a video. Visiting the site produces a message saying that you don’t have the correct codec installed to watch the video whereupon the site offers you a DMG file for Apple Macs.
Ironically Apple issued a support advisory in 2008 urging customers to run anti-virus software – but after media interest, rapidly deleted the page from their website.

Online video was a major conduit for Mac malware in 2009.
- Sophos reported on how hackers were planting versions of the RSPlug Trojan horse on websites, posing as an HDTV program called MacCinema.
- Hackers planted a version of the Jahlav Mac Trojan horse on a website posing as a portal for hardcore porn videos.
- The Twitter account of celebrity blogger Guy Kawasaki had a malicious link posted onto it, claiming to point to a sex video of Gossip Girl actress Leighton Meester. In reality, however, the link leads unsuspecting users to malware that could infect Mac users.
 In 2009 Apple finally began to build some rudimentary anti-malware protection into Mac OS X. Although it wasn’t really equal to a true anti-virus product (it only protected against a handful of Mac malware, doesn’t defend you if you try to copy an infected file from a USB stick for instance, and doesn’t offer clean-up facilities), it was still encouraging to see some attempt to offer more protection for Mac users.
In 2009 Apple finally began to build some rudimentary anti-malware protection into Mac OS X. Although it wasn’t really equal to a true anti-virus product (it only protected against a handful of Mac malware, doesn’t defend you if you try to copy an infected file from a USB stick for instance, and doesn’t offer clean-up facilities), it was still encouraging to see some attempt to offer more protection for Mac users.
2010 – Throughout 2010 Mac malware was distributed disguised as a legitimate application.
- The OSX/Pinhead Trojan (aka HellRTS) was disguised as iPhoto, the photo application which ships on modern Macs. The backdoor Trojan horse can allow hackers to gain remote control over your iMac or MacBook.
 A Java applet distributed via Facebook (FB) was used to target not just Windows computers but Mac OS X and Linux too. The Boonana cross-platform worm appeared, disguised as a video and runs in the background, and reports system information to servers on the Internet, which can be a big breach of personal information. The Trojan also attempts to spread itself by sending messages from the user account to other people through spam.
A Java applet distributed via Facebook (FB) was used to target not just Windows computers but Mac OS X and Linux too. The Boonana cross-platform worm appeared, disguised as a video and runs in the background, and reports system information to servers on the Internet, which can be a big breach of personal information. The Trojan also attempts to spread itself by sending messages from the user account to other people through spam.
- A piece of Mac spyware called Spynion (also known as OpinionSpy or PremierOpinion) came to light, attached to screen savers and other add-ons for users’ Macs. it’s a variant of Windows spyware that has existed since 2008. Spynion would take advantage of users not properly reading End User License Agreements (EULAs), allowing it to spy on browsing habits and search behavior.
In late 2010, Sophos issued a free anti-virus for Mac home users. Early reports indicated that there are plenty of Mac users with malware on their computers – some of it Windows malware, some Mac OS X, and some cross-platform. The author states that there’s no doubt that the Windows malware problem is much larger than the Mac threat, but that doesn’t mean that the danger of malware infection on Mac OS X is non-existent.
The events of 2011 would make it clearer to Mac users than ever before that the malware threat was real..
Related articles
- Malware Targets Macs and Windows PCs (onecoolsitebloggingtips.com)
Ralph Bach has been in IT long enough to know better and has blogged from his Bach Seat about IT, careers, and anything else that catches his attention since 2005. You can follow him on LinkedIn, Facebook, and Twitter. Email the Bach Seat here.





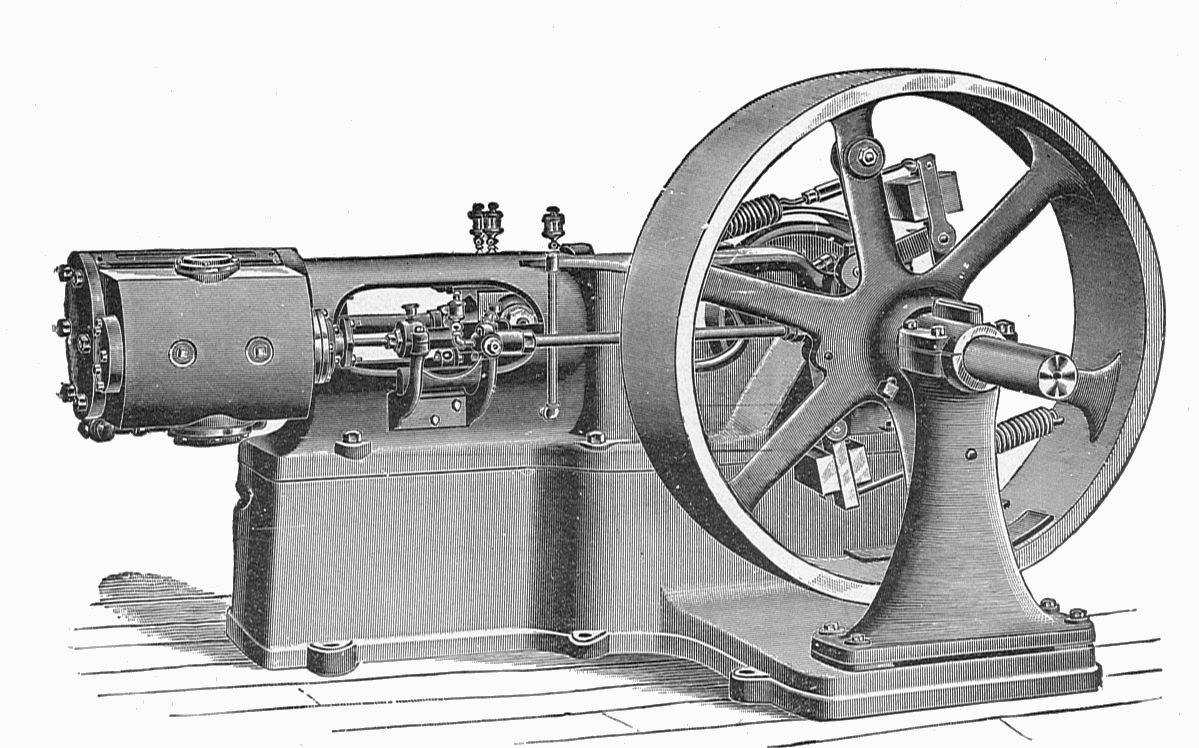





 I recall as a newbie techie the first time I had to be in on Sunday morning to work with the site engineer to crank up the 100 HP Cummins standby generator. The firm ran the monthly test to make sure the critical systems stayed up. The generator was enclosed in a secure room that contained the heat and noise. The exhaust was vented out. One of my regular jobs was to kick the standby 55-gallon drum of diesel with the hand pump on it to make sure there was fuel available for the generator.
I recall as a newbie techie the first time I had to be in on Sunday morning to work with the site engineer to crank up the 100 HP Cummins standby generator. The firm ran the monthly test to make sure the critical systems stayed up. The generator was enclosed in a secure room that contained the heat and noise. The exhaust was vented out. One of my regular jobs was to kick the standby 55-gallon drum of diesel with the hand pump on it to make sure there was fuel available for the generator. Updated 01-19-13 The student
Updated 01-19-13 The student 


