ComputerWorld defines post-PC devices like a tablet with four characteristics;
1. It’s an appliance.
2. It’s got a multi-touch UI,
3. It doesn’t have file management,
4. Apps function on the app-store model.
Big Drop in Tablet Average Selling Price
 The Business Insider has documented the average selling price (ASP) of tablets keeps falling. The ASP fell 17 percent from 2010—when it was pretty much just the Apple (AAPL) iPad—to 2011. Through the first six months of this year alone, the ASP has fallen another 17 percent.
The Business Insider has documented the average selling price (ASP) of tablets keeps falling. The ASP fell 17 percent from 2010—when it was pretty much just the Apple (AAPL) iPad—to 2011. Through the first six months of this year alone, the ASP has fallen another 17 percent.
The drop is driven partly by the introduction of $200 mini tablets like the Amazon (AMZN) Kindle Fire, but also a fall in the price of the dominant large-screen devices.
rb- No wonder Apple is suing everybody in sight to prevent competition. They need to protect their profit margins. Way to go USPTO.
Are We in the Post PC Era
 Kevin C. Tofel at GigaOM recently wrote that by looking at the numbers, it’s difficult to argue that the Apple (AAPL) iPad is anything less than a success. The company sold more iPads — 15.4 million — than any traditional computer maker sold PCs in the last quarter of 2011. Mr. Tofel argues what is debatable, however, is whether the iPad will take us to the “post-PC” era, as Apple calls it. Former Apple director Michael Mace suggests that the PC isn’t going away, agreeing with Apple’s CEO, Tim Cook, who recently said “I don’t predict the demise of the PC industry, I don’t subscribe to that.”
Kevin C. Tofel at GigaOM recently wrote that by looking at the numbers, it’s difficult to argue that the Apple (AAPL) iPad is anything less than a success. The company sold more iPads — 15.4 million — than any traditional computer maker sold PCs in the last quarter of 2011. Mr. Tofel argues what is debatable, however, is whether the iPad will take us to the “post-PC” era, as Apple calls it. Former Apple director Michael Mace suggests that the PC isn’t going away, agreeing with Apple’s CEO, Tim Cook, who recently said “I don’t predict the demise of the PC industry, I don’t subscribe to that.”
Michael Mace observed on his personal blog that. “I think the ‘PC era’ meme from Apple is self-serving hype. Of course, they want to convince you that the world is shifting away from a market where Apple has less than 10% worldwide share to a market where Apple has well over 50% share.”
“... My thought is that PCs aren’t going to suddenly disappear, but people will continue to opt for capable tablets or hybrid devices in the place of future, new PC purchases. The mobile market is shifting traditional tasks away from PCs of old, and for people who need a PC occasionally, they will likely be able to access one remotely.”
“Apple is simply calling out the post-PC era because it has successfully transformed its business lines ahead of the curve and before its peers.“
Mr. Tofel points out that when all is said and done, Mace makes one last salient point worth noting: How will Microsoft (MSFT) respond to the iPad? We know the answer is Windows 8, but there’s still an open question about how well the platform will do on tablets. Perhaps, Mace notes, we’re not exactly on the cusp of a post-PC age, but instead, a post-Microsoft era.
Related articles:
- Amazing Stats from Apple Q3 Earnings Prove Yet Again We’re In A Post-PC Era
Magic Cable Trio All-in-One USB Simplicity
 Tested.com points out the handy Innergie Magic Cable Trio which solves an age-old problem. You never have the right USB connector when you need it. The Magic Cable Trio combines mini USB, micro USB, and 40-pin dock tips into a single cable. The handy-dandy cable will play ball with your tablet, or just about any USB device you can get your hands on according to Tested. It won’t work with printers, but the Magic Cable Trio is meant for plug-and-play accessibility, not languishing behind a desk collecting dust.
Tested.com points out the handy Innergie Magic Cable Trio which solves an age-old problem. You never have the right USB connector when you need it. The Magic Cable Trio combines mini USB, micro USB, and 40-pin dock tips into a single cable. The handy-dandy cable will play ball with your tablet, or just about any USB device you can get your hands on according to Tested. It won’t work with printers, but the Magic Cable Trio is meant for plug-and-play accessibility, not languishing behind a desk collecting dust.
The tips are all attached and fold out-of-the-way when not in use. Tested says the extra tips could be a bit of a nuisance, but you’ll never have to worry about losing the adapters in the bottom of a backpack. The Magic Cable Trio costs $20 at Innergie’s store.
Related articles
- 100W over USB is here with the new Power Delivery spec (semiaccurate.com)
Polycom on iPad
 Analysts are forecasting that the tablet market will grow five-fold by 2015 to 320 million units sold annually. The cumulative number of tablets in use by that point will be about 900 million. Many are predicting that the tablet will continue to gain in functionality and take over the laptop in the coming years.
Analysts are forecasting that the tablet market will grow five-fold by 2015 to 320 million units sold annually. The cumulative number of tablets in use by that point will be about 900 million. Many are predicting that the tablet will continue to gain in functionality and take over the laptop in the coming years.
Polycom is pioneering high-definition video collaboration for tablets called Polycom® RealPresence™ Mobile. Polycom RealPresence Mobile is the first enterprise tablet software that lets mobile users enjoy HD video collaboration from anywhere. It is available now on the Apple (AAPL) iPad 2, MotorolaXOOM, and Samsung (005930) Galaxy Tab 10.1—with more mobile devices to follow.
RealPresence Mobile extends Polycom’s HD video collaboration technology beyond the office and conference room. Iy bringing a high-quality, secure, reliable experience to tablets that is comparable to desktop and room systems.
RealPresence Mobile delivers enterprise video collaboration for the business tablet market and delivers provisioning, management, system interoperability, firewall traversal, and scalability that CIOs need, and the reliability, security, rich features, and lifelike quality that users demand.
RealPresence Mobile scales, supporting up to 75,000 devices and 25,000 concurrent calls.
You can find download a free end-user application from the Apple Store, Android Market, and Samsung Apps.
Related articles
- Polycom Brings Video Meetings to IPads, Android Tablets (pcworld.com)
Ralph Bach has been in IT long enough to know better and has blogged from his Bach Seat about IT, careers, and anything else that catches his attention since 2005. You can follow him on LinkedIn, Facebook, and Twitter. Email the Bach Seat here.












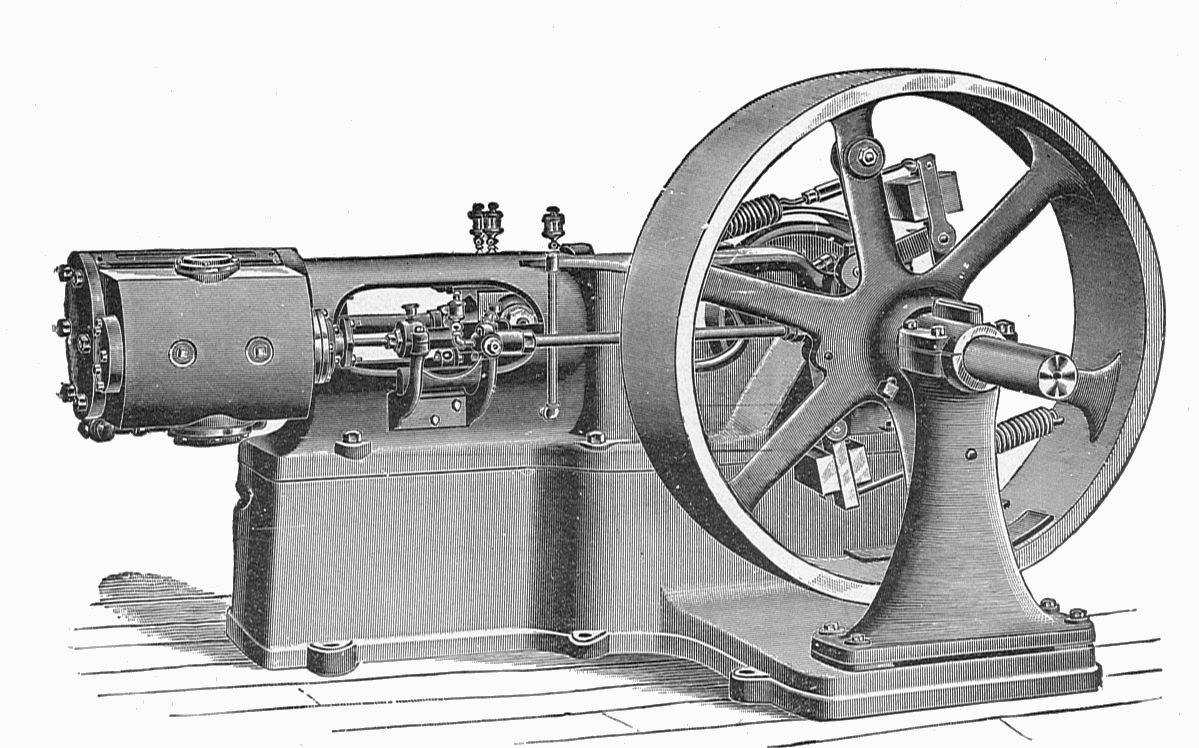





 I recall as a newbie techie the first time I had to be in on Sunday morning to work with the site engineer to crank up the 100 HP Cummins standby generator. The firm ran the monthly test to make sure the critical systems stayed up. The generator was enclosed in a secure room that contained the heat and noise. The exhaust was vented out. One of my regular jobs was to kick the standby 55-gallon drum of diesel with the hand pump on it to make sure there was fuel available for the generator.
I recall as a newbie techie the first time I had to be in on Sunday morning to work with the site engineer to crank up the 100 HP Cummins standby generator. The firm ran the monthly test to make sure the critical systems stayed up. The generator was enclosed in a secure room that contained the heat and noise. The exhaust was vented out. One of my regular jobs was to kick the standby 55-gallon drum of diesel with the hand pump on it to make sure there was fuel available for the generator.



