 Graham Cluley at Sophos recently wrote an excellent history of Apple Macintosh malware. He points out that Mac malware is a subject that raises strong emotions. There are some who believe that the problem is over-hyped and others who believe that the malware problem on Macs is underestimated by the Apple-loving community. The author writes that hopefully, this short history will go some way to present the facts and encourage sensible debate. (rb- We have just taken on a new customer which is 85% Mac and 15% PC. I have had this very conversation with my Apple certified tech who does the field support.)
Graham Cluley at Sophos recently wrote an excellent history of Apple Macintosh malware. He points out that Mac malware is a subject that raises strong emotions. There are some who believe that the problem is over-hyped and others who believe that the malware problem on Macs is underestimated by the Apple-loving community. The author writes that hopefully, this short history will go some way to present the facts and encourage sensible debate. (rb- We have just taken on a new customer which is 85% Mac and 15% PC. I have had this very conversation with my Apple certified tech who does the field support.)
Click here for part two of this series. Click here to read my recent series commemorating the 25th anniversary of the computer virus.
 1982 – Apple II – The first virus to affect Apple computers wasn’t written for the Macintosh (the original Mac did appear until 1984). 15-year-old student Rich Skrenta wrote the Elk Cloner virus, capable of infecting the boot sector of Apple II computers. On every 50th boot the Elk Cloner virus would display a short poem:
1982 – Apple II – The first virus to affect Apple computers wasn’t written for the Macintosh (the original Mac did appear until 1984). 15-year-old student Rich Skrenta wrote the Elk Cloner virus, capable of infecting the boot sector of Apple II computers. On every 50th boot the Elk Cloner virus would display a short poem:
It will get on all your disks
It will infiltrate your chips
Yes, it’s Cloner!
It will stick to you like glue
It will modify RAM too
Send in the Cloner!
The blog says many Apple fans are surprised that the Elk Cloner boot sector virus predates IBM (IBM) PC viruses by some years. (I got my first paying tech job using an Apple II and PFS:File to build a database).
1987 – Macintosh – The nVIR virus began to infect Apple Macintosh computers, spreading its malware mainly by floppy disk. It was a similar story to what was happening in the world of MS-DOS malware, where viruses would typically travel from computer to computer by users sharing floppy disks.
Source code for nVIR was later made available, causing a rash of variants for the Mac platform. The author writes that the first anti-virus products for Mac, some free, some commercial, began to emerge in response th this malware. (In my first tech support Job, I got very familiar with the Mac 30/SE, since there was a computer lab full of them with a SCSI chain from the Mac to an external hard drive to a scanner. They also printed to a LaserWriter 2 with AppleTalk and Phonenet. I still have a bag of terminators.)
 1988 – HyperCard – Running on early versions of Apple’s Mac OS, one HyperCard virus displayed a message about Michael Dukakis’s US presidential bid before self-destructing:
1988 – HyperCard – Running on early versions of Apple’s Mac OS, one HyperCard virus displayed a message about Michael Dukakis’s US presidential bid before self-destructing:
“Greetings from the HyperAvenger! I am the first HyperCard virus ever. I was created by a mischievous 14-year-old, and am completely harmless. Dukakis for preseident (sic) in ’88. Peace on earth and have a nice day”
1990 – The MDEF virus (aka Garfield) emerged, spreading malware on application and system files on the Mac.
1991 – HC (also known as Two Tunes or Three Tunes) was a HyperCard virus discovered in Holland and Belgium in March 1991. The writes that on German language versions of the operating system it would play German folk tunes and display messages such as “Hey, what are you doing?” and “Don’t panic.”
 1995 – Concept Macro Virus – Microsoft (MSFT) accidentally shipped the first-ever Word macro virus, Concept, on CD-ROM. It infected both Macs and PCs running Microsoft Word. Concept was not written with malicious intent but thousands of macro viruses were to follow, many also affecting Microsoft Office for Mac. Word macro viruses turned the world of Mac *and* Windows malware on its head overnight according to Sophos.
1995 – Concept Macro Virus – Microsoft (MSFT) accidentally shipped the first-ever Word macro virus, Concept, on CD-ROM. It infected both Macs and PCs running Microsoft Word. Concept was not written with malicious intent but thousands of macro viruses were to follow, many also affecting Microsoft Office for Mac. Word macro viruses turned the world of Mac *and* Windows malware on its head overnight according to Sophos.
Macro viruses are written in an easy-to-understand macro language that Microsoft included in its Office programs making it. The blog says the macro language made it child’s play to create new malware variants. Most people at the time considered documents to be non-dangerous and were happy to receive them without thinking about the security risks. Just opening a Word .DOC file could infect your computer because the macro virus’s code was embedded within.
1996 – Laroux Excel macro virus – The Laroux virus did not affect Mac users until Microsoft released Excel 98 for Mac and then Apple users could also become victims.
 1998 – Hong Kong introduced the next significant Mac malware outbreak the blog says. It was first spotted in the wild in Hong Kong. The worm – dubbed AutoStart 9805 – spread rapidly in the desktop publishing community via removable media, using the CD-ROM AutoPlay feature of QuickTime 2.5+. (rb- An AutoPlay issue – whoda thunkit?). In the same year, Sevendust, also known as 666, infected applications on Apple Mac computers.
1998 – Hong Kong introduced the next significant Mac malware outbreak the blog says. It was first spotted in the wild in Hong Kong. The worm – dubbed AutoStart 9805 – spread rapidly in the desktop publishing community via removable media, using the CD-ROM AutoPlay feature of QuickTime 2.5+. (rb- An AutoPlay issue – whoda thunkit?). In the same year, Sevendust, also known as 666, infected applications on Apple Mac computers.
After 1988 Mr. Cluely writes that big changes to the Mac malware scene were just around the corner. The release of Mac OS X, a whole new operating system which would mean that much of the old malware would no longer be capable of running. Mac-specific malware would have to be written with a new OS in mind.
Related articles
Ralph Bach has been in IT long enough to know better and has blogged from his Bach Seat about IT, careers, and anything else that catches his attention since 2005. You can follow him on LinkedIn, Facebook, and Twitter. Email the Bach Seat here.
 The BusinessInsider published some awesome charts from Horace Dediu of Asymco that shows the collapse of Microsoft (MSFT) and Intel’s (INTC) monopoly in personal computing. Henry Blodget says the chart shows how Google‘s (GOOG) Android and Apple (AAPL) have successfully eaten into Wintel‘s market share. Is it the end of Microsoft?
The BusinessInsider published some awesome charts from Horace Dediu of Asymco that shows the collapse of Microsoft (MSFT) and Intel’s (INTC) monopoly in personal computing. Henry Blodget says the chart shows how Google‘s (GOOG) Android and Apple (AAPL) have successfully eaten into Wintel‘s market share. Is it the end of Microsoft?


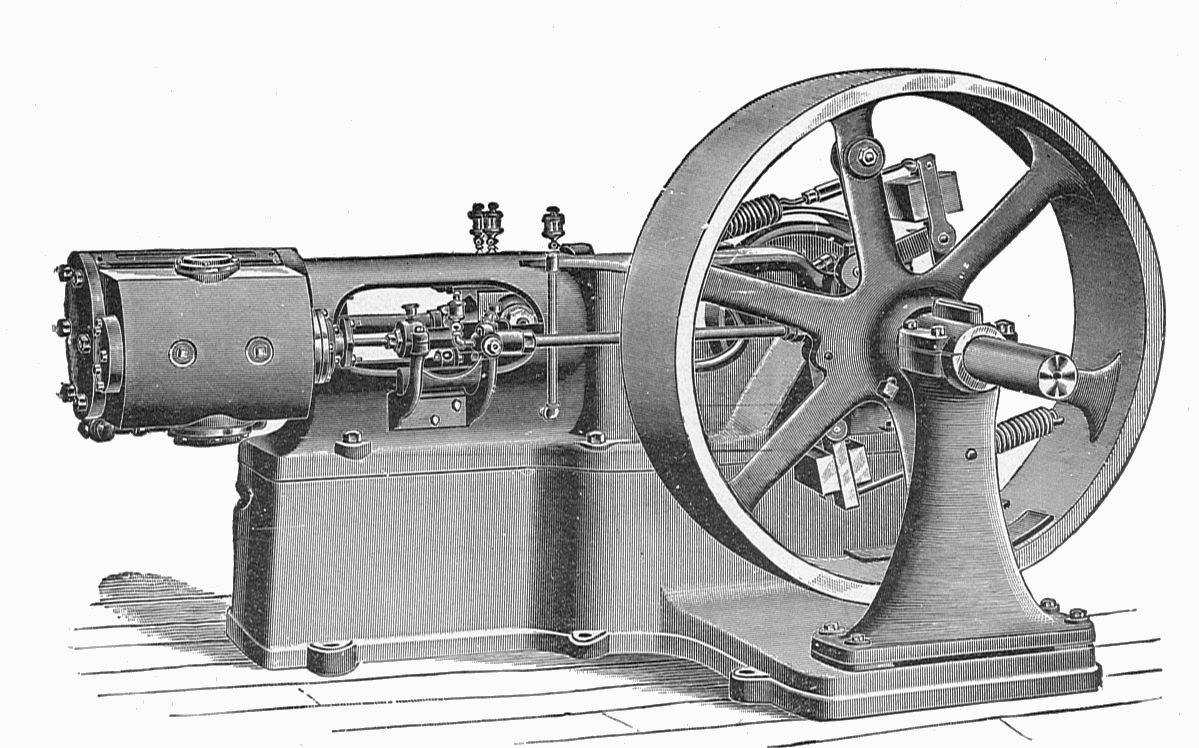





 I recall as a newbie techie the first time I had to be in on Sunday morning to work with the site engineer to crank up the 100 HP Cummins standby generator. The firm ran the monthly test to make sure the critical systems stayed up. The generator was enclosed in a secure room that contained the heat and noise. The exhaust was vented out. One of my regular jobs was to kick the standby 55-gallon drum of diesel with the hand pump on it to make sure there was fuel available for the generator.
I recall as a newbie techie the first time I had to be in on Sunday morning to work with the site engineer to crank up the 100 HP Cummins standby generator. The firm ran the monthly test to make sure the critical systems stayed up. The generator was enclosed in a secure room that contained the heat and noise. The exhaust was vented out. One of my regular jobs was to kick the standby 55-gallon drum of diesel with the hand pump on it to make sure there was fuel available for the generator.






 It is up to operating system vendors to choose which IP address assignment method will be the default on their devices. The author says that some vendors have made good choices, particularly within the last year. Microsoft has long led the charge on IPv6 privacy, with privacy extensions on by default in all versions of
It is up to operating system vendors to choose which IP address assignment method will be the default on their devices. The author says that some vendors have made good choices, particularly within the last year. Microsoft has long led the charge on IPv6 privacy, with privacy extensions on by default in all versions of 


 Help Net Security explains the malware triggers the massive printing by exploiting the Windows default print spooler directory. “During the infection phase, a .spl file is created in [DRIVE_LETTER]system32Spool PRINTERS[RANDOM].spl. Note the Windows’ default print spooler directory is %System%spoolprinters.”
Help Net Security explains the malware triggers the massive printing by exploiting the Windows default print spooler directory. “During the infection phase, a .spl file is created in [DRIVE_LETTER]system32Spool PRINTERS[RANDOM].spl. Note the Windows’ default print spooler directory is %System%spoolprinters.”